How to Disable VMware Plugins in vCenter Server per VMSA-2021-0002, VMSA-2021-0010, VMSA-2021-0010
Article ID: 317705
Updated On:
Products
VMware vCenter Server
Issue/Introduction
Vulnerabilities in plugins that ship with vCenter Server have been disclosed by VMware. These vulnerabilities and their impact on VMware products are documented in the following VMware Security Advisories (VMSAs), please review these documents before continuing:
VMware has investigated these issues and has determined that the possibility of exploitation can be removed via disablement of impacted plugins by performing the steps detailed in the Workaround section of this article.
- CVE-2021-21972 - VMSA-2021-0002 (vRealize Operations Manager Plugin)
- CVE-2021-21985 - VMSA-2021-0010 (Virtual SAN Health Check Plugin)
- CVE-2021-21986 - VMSA-2021-0010 (Virtual SAN Health Check, Site Recovery, vSphere Lifecycle Manager, and VMware Cloud Director Availability Plugins)
VMware has investigated these issues and has determined that the possibility of exploitation can be removed via disablement of impacted plugins by performing the steps detailed in the Workaround section of this article.
Resolution
The workarounds described in this document are meant to be a temporary solution only.
Upgrades documented in the aforementioned advisories should be applied to resolve vulnerabilities in impacted plugins.
Workaround:
Important: Plugins must be set to "incompatible." Disabling a plugin from within the UI does not prevent exploitation.
The following actions must be performed on both the active and passive nodes in environments running vCenter High Availability (VCHA).
The examples documented here show the steps to disable all plugins which have been impacted by vulnerabilities disclosed by VMware. Depending on your environment and your requirements, you may only want to only disable a subset of these plugins.
Please see the VMSA-2021-0010: What You Need to Know blog to determine the plugins that are required to be disabled in your configuration.
Add the lines below to the compatibility-matrix.xml file to disable each individual plugin:
Some plugins are enabled by default, and these default plugins differ from version to version.
Please refer to the table below to determine which plugin is enabled by default and which plugin requires the associated product to be installed and configured.
Default = Plugin is enabled by default on all vCenter installations
To implement the workaround, follow the steps applicable for your type of vCenter Server deployment.
Quick links:
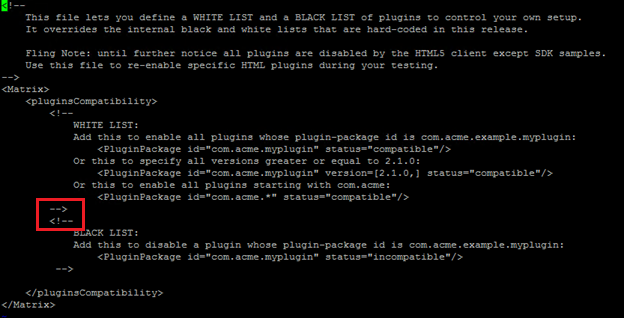
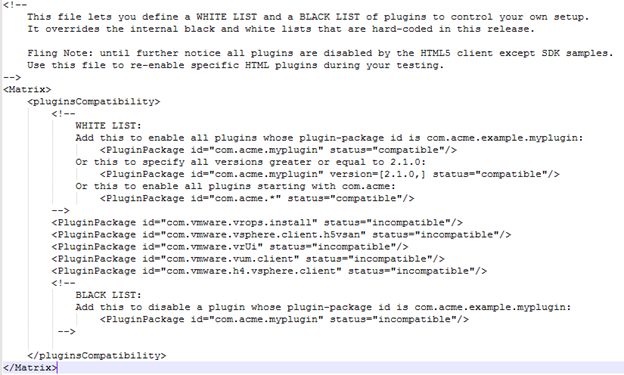
Note: Content of an unedited file should look similar to the following:
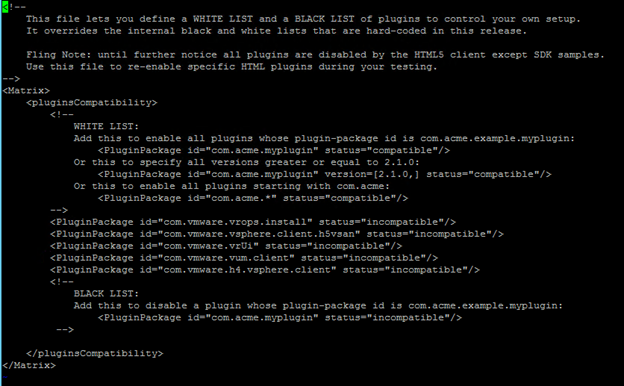
Note: The file should like below:
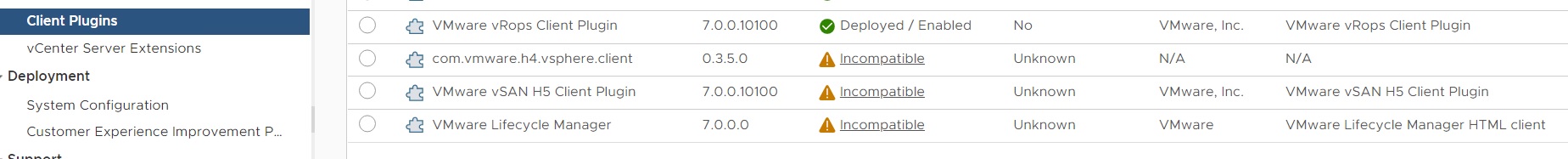
From the vSphere Client (HTML5), the VMware Virtual SAN Health Check Plugin can be seen as incompatible under Administration > Solutions > client-plugins as shown below:
For vSphere 7.0:
For vSphere 6.7:
Note: The file should look like below:
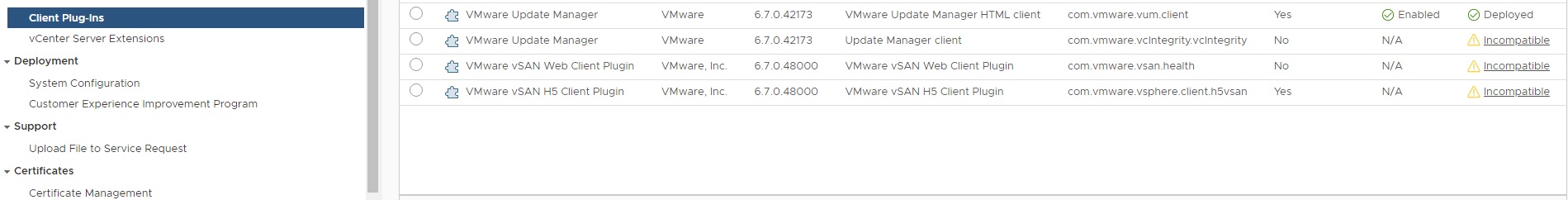
From the vSphere Client (HTML 5), the disabled plugins can be seen as incompatible under Administration > Solutions > client-plugins as shown below:

Upgrades documented in the aforementioned advisories should be applied to resolve vulnerabilities in impacted plugins.
Workaround:
Important: Plugins must be set to "incompatible." Disabling a plugin from within the UI does not prevent exploitation.
The following actions must be performed on both the active and passive nodes in environments running vCenter High Availability (VCHA).
The examples documented here show the steps to disable all plugins which have been impacted by vulnerabilities disclosed by VMware. Depending on your environment and your requirements, you may only want to only disable a subset of these plugins.
Please see the VMSA-2021-0010: What You Need to Know blog to determine the plugins that are required to be disabled in your configuration.
Add the lines below to the compatibility-matrix.xml file to disable each individual plugin:
| Plugin Name | Configuration Line |
| VMware vRops Client Plugin | <PluginPackage id="com.vmware.vrops.install" status="incompatible"/> |
| VMware vSAN H5 Client Plugin | <PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/> |
| Site Recovery | <PluginPackage id="com.vmware.vrUi" status="incompatible"/> |
| VMware vSphere Life-cycle Manager | <PluginPackage id="com.vmware.vum.client" status="incompatible"/> |
| VMware Cloud Director Availability | <PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/> |
Some plugins are enabled by default, and these default plugins differ from version to version.
Please refer to the table below to determine which plugin is enabled by default and which plugin requires the associated product to be installed and configured.
Default = Plugin is enabled by default on all vCenter installations
Product = Plugin is enabled only when the associated product is installed and configured
| vCenter Version | vRealize Operations | vSAN | VMware vSphere Life-cycle Manager | Site Recovery | VMware Cloud Director Availability |
| 6.5 | Default | Default (6.5 U3k and later) | N/A | Product | Product |
| 6.7 | Default | Default | N/A | Product | Product |
| 7.0 | Default | Default | Default | Product | Default |
To implement the workaround, follow the steps applicable for your type of vCenter Server deployment.
Quick links:
- Disable vCenter Server plugins on Linux-based virtual appliances (vCSA)
- Disable vCenter Server plugins on Windows-based vCenter Server deployment
Disable vCenter Server plugins on Linux-based virtual appliances (vCSA)
- Connect to the vCSA using an SSH session and root credentials.
- Backup the /etc/vmware/vsphere-ui/compatibility-matrix.xml file:
cp -v /etc/vmware/vsphere-ui/compatibility-matrix.xml /etc/vmware/vsphere-ui/compatibility-matrix.xml.backup
- Open the compatibility-matrix.xml file in a text editor:
vi /etc/vmware/vsphere-ui/compatibility-matrix.xml
Note: Content of an unedited file should look similar to the following:
- To disable all plugins with disclosed vulnerabilities, add the following lines as shown below:
Note: These entries should be added between the --> and <!— entries highlighted above.
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
Note: The file should like below:
- Save and close the compatibility-matrix.xml file:
:wq!
- Stop and restart the vsphere-ui service using these commands:
service-control --stop vsphere-ui
service-control --start vsphere-ui
service-control --start vsphere-ui
From the vSphere Client (HTML5), the VMware Virtual SAN Health Check Plugin can be seen as incompatible under Administration > Solutions > client-plugins as shown below:
For vSphere 6.7:
Disable vCenter Server plugins on Windows-based vCenter Server deployments
- RDP to the windows based vCenter Server.
- Take a backup of the C:\ProgramData\VMware\vCenterServer\cfg\vsphere-ui\compatibility-matrix.xml file.
- Open the compatibility-matrix.xml file in a text editor:
Note: Content of an unedited file should look similar to the following:
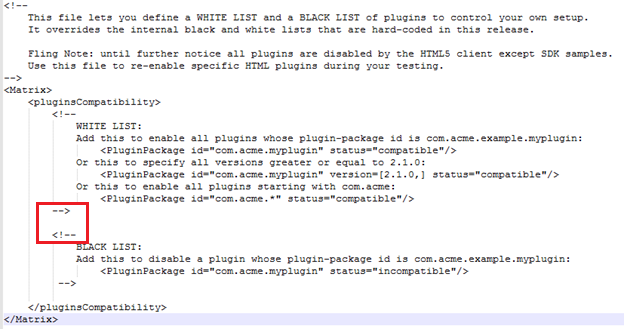
- To disable all plugins with disclosed vulnerabilities, add the following lines as shown below:
Note: These entries should be added between the --> and <!— entries highlighted above
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
Note: The file should look like below:
- Save and close the file.
- In a Windows command prompt, stop and restart the vsphere-ui service using these commands:
C:\Program Files\VMware\vCenter Server\bin> service-control --stop vsphere-ui
C:\Program Files\VMware\vCenter Server\bin> service-control --start vsphere-ui
C:\Program Files\VMware\vCenter Server\bin> service-control --start vsphere-ui
From the vSphere Client (HTML 5), the disabled plugins can be seen as incompatible under Administration > Solutions > client-plugins as shown below:
Additional Information
For up-to-date information as well as future security information please sign up for VMware Security Advisory announcements at our mailing list portal. RSS feeds are also available on the advisories themselves.
Revert the Workaround
To revert the workaround, follow the steps applicable for your type of vCenter Server deployment.
Quick links:
Impact/Risks:
Functionality impacts are limited to environments that utilize VMware plugins. Disablement of these plugins will result in a loss of management and monitoring capabilities provided by the plugins.
Revert the Workaround
To revert the workaround, follow the steps applicable for your type of vCenter Server deployment.
Quick links:
- Revert the workaround on Linux-based virtual appliances (vCSA)
- Revert the workaround on Windows-based vCenter Server deployments
Revert the workaround on Linux-based virtual appliances (vCSA)
- Connect to the vCSA with an SSH session and root credentials.
- Open the compatibility-matrix.xml file in a text editor:
vi /etc/vmware/vsphere-ui/compatibility-matrix.xml
- Remove the below line in the file.
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
- Save and close the file:
:wq!
- Stop and restart the vsphere-ui service using these commands:
- service-control --stop vsphere-ui.
- service-control --start vsphere-ui
- Validate that the vsphere-ui service is up.
- How to Stop, Start or Restart vCenter Server 6.x Services
- Stopping, Starting or Restarting VMware vCenter Server Appliance 6.x & above services
Revert the workaround on Windows-based vCenter Server deployments
- Connect to the Windows vCenter Server.
- Open C:\ProgramData\VMware\vCenterServer\cfg\vsphere-ui\compatibility-matrix.xml using a text editor.
- Remove the below line in the file.
<PluginPackage id="com.vmware.vrops.install" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
<PluginPackage id="com.vmware.vsphere.client.h5vsan" status="incompatible"/>
<PluginPackage id="com.vmware.vrUi" status="incompatible"/>
<PluginPackage id="com.vmware.vum.client" status="incompatible"/>
<PluginPackage id="com.vmware.h4.vsphere.client" status="incompatible"/>
- Save and close the file.
- In a Windows command prompt, stop and restart the vsphere-ui service using these commands:
- C:\Program Files\VMware\vCenter Server\bin> service-control --stop vsphere-ui
- C:\Program Files\VMware\vCenter Server\bin> service-control --start vsphere-ui
- Validate that the vsphere-ui service is up.
- How to Stop, Start or Restart vCenter Server 6.x Services
- Stopping, Starting or Restarting VMware vCenter Server Appliance 6.x & above services
Impact/Risks:
Functionality impacts are limited to environments that utilize VMware plugins. Disablement of these plugins will result in a loss of management and monitoring capabilities provided by the plugins.
Feedback
Yes
No
